Picture this: you’re scrolling through social media when an ad for those expensive sneakers you’ve been eyeing pops up, priced at an unbelievable 80% off. Your heart races as you click the link, but a nagging thought suddenly hits you—how to check if a website is safe before handing over your credit card details? It’s a scenario almost everyone has faced, hovering your mouse over a link and wondering if it’s going to lead to a sweet deal or a complete disaster.
The truth is, cybercriminals are getting smarter every single day, creating duplicate storefronts and malicious links that look virtually identical to the real thing. This growing threat of online fraud means that relying purely on your gut feeling is no longer enough to protect your hard-earned money and personal data. Every internet user, regardless of their technical skills, needs to understand how to navigate around these digital traps.
In this guide, you will learn exactly what to look for before you ever hit that checkout button or type in your password. We’ll break down the warning signs of fraudulent pages and give you simple, actionable tools you can use immediately. By the time you finish reading, you’ll have the confidence to browse, shop, and click without fear.
Look Beyond the Padlock: The Basics of HTTPS
For years, we were taught that a simple visual check was enough to guarantee our security. While looking at your browser’s address bar is a great first step, it is only part of the puzzle.
What HTTPS Actually Means
When you look at a web address, you should see HTTPS rather than just HTTP. That extra “S” stands for “Secure.” It indicates that the site has an active SSL Certificate, which encrypts the data passing between your computer and the website’s server. When this encryption is active, you will typically see a little Padlock Icon next to the URL.
However, you need to know a very important caveat:
“A secure padlock doesn’t guarantee a safe site; it just guarantees your connection to that site is encrypted. Cybercriminals use encryption too, which is why verifying the actual domain is critical to your online safety.” — National Cybersecurity Alliance
Because scammers can easily obtain an SSL Certificate for a fake site, seeing the Padlock Icon doesn’t mean the people running the site are honest. It just means the data you send them—like your credit card numbers—is securely transmitted to the scammers.
How to Check If a Website Is Safe Using Dedicated Tools
When your eyes deceive you, let technology do the heavy lifting. If you are wondering how to tell if a website is legit, your best bet is to use an automated website safety checker. These tools scan URLs against massive databases of known threats.
Top Safety Checkers You Can Use Right Now
- Google Safe Browsing: This is a fantastic, free tool provided by Google. You simply paste the URL into their transparency report page, and it will instantly tell you if the site is currently hosting anything dangerous.
- VirusTotal: If you want a deep dive, this is your go-to platform. VirusTotal analyzes suspicious files and URLs to detect types of Malware and malicious breaches. It aggregates data from dozens of antivirus scanners into one easy-to-read report.
- URLVoid: This service cross-references a website against multiple blacklist engines. It gives you a detailed safety report and helps you quickly spot malicious behavior.
- Norton Safe Web: Powered by a trusted name in cybersecurity, this tool analyzes sites to see how they will affect your computer. It checks for computer threats, identity threats, and annoyance factors.
Whenever you feel a spike of doubt, pause and run the link through a website safety checker. It takes five seconds and could save you hours of headaches.
Investigate the Domain Age and Registration
Scam websites usually don’t last very long. Cybercriminals set them up, rip people off, and abandon them as soon as they get caught or blocked by internet service providers. Because of this “burn and churn” tactic, checking a site’s history is incredibly revealing.
Why Domain Age Matters
If you are looking at an online store claiming to have thousands of five-star reviews, but you find out the website was registered just three days ago, you have spotted a major red flag. Checking the Domain Age is a foolproof way to verify a company’s claims. You can use free “WHOIS” lookup tools online to see exactly when a domain was registered and who owns it. Legitimate businesses generally have older, established domain histories.
Trust Your Eyes: How to Spot a Fake Website
Sometimes, the best defense against digital threats is plain old common sense. Phishing attacks rely heavily on creating a sense of urgency and hoping you don’t look too closely at the details. If you slow down, the cracks in their facade become obvious.
Red Flags to Watch For
- Weird URLs: Scammers love to use typosquatting. You might think you are visiting “amazon.com,” but a closer look reveals you are actually on “arnazon.com” (using an ‘r’ and an ‘n’). Always double-check the spelling in the address bar.
- Poor Grammar and Spelling: Legitimate companies have editors and marketing teams. If a homepage is riddled with awkward phrasing, weird formatting, and obvious spelling mistakes, close the tab immediately.
- Unbelievable Deals: We all love a bargain, but if a brand new laptop is selling for $40, you aren’t getting a deal—you are getting robbed.
- Strange Payment Methods: If an online retailer insists you pay via wire transfer, cryptocurrency, or gift cards, walk away. These methods are untraceable and non-refundable.
If you are ever unsure about how to check if a website is safe, take a step back and evaluate the overall quality of the page. If it feels cheap, rushed, or overly aggressive in demanding your personal info, it is likely a scam.
Protect Your Devices from Hidden Threats
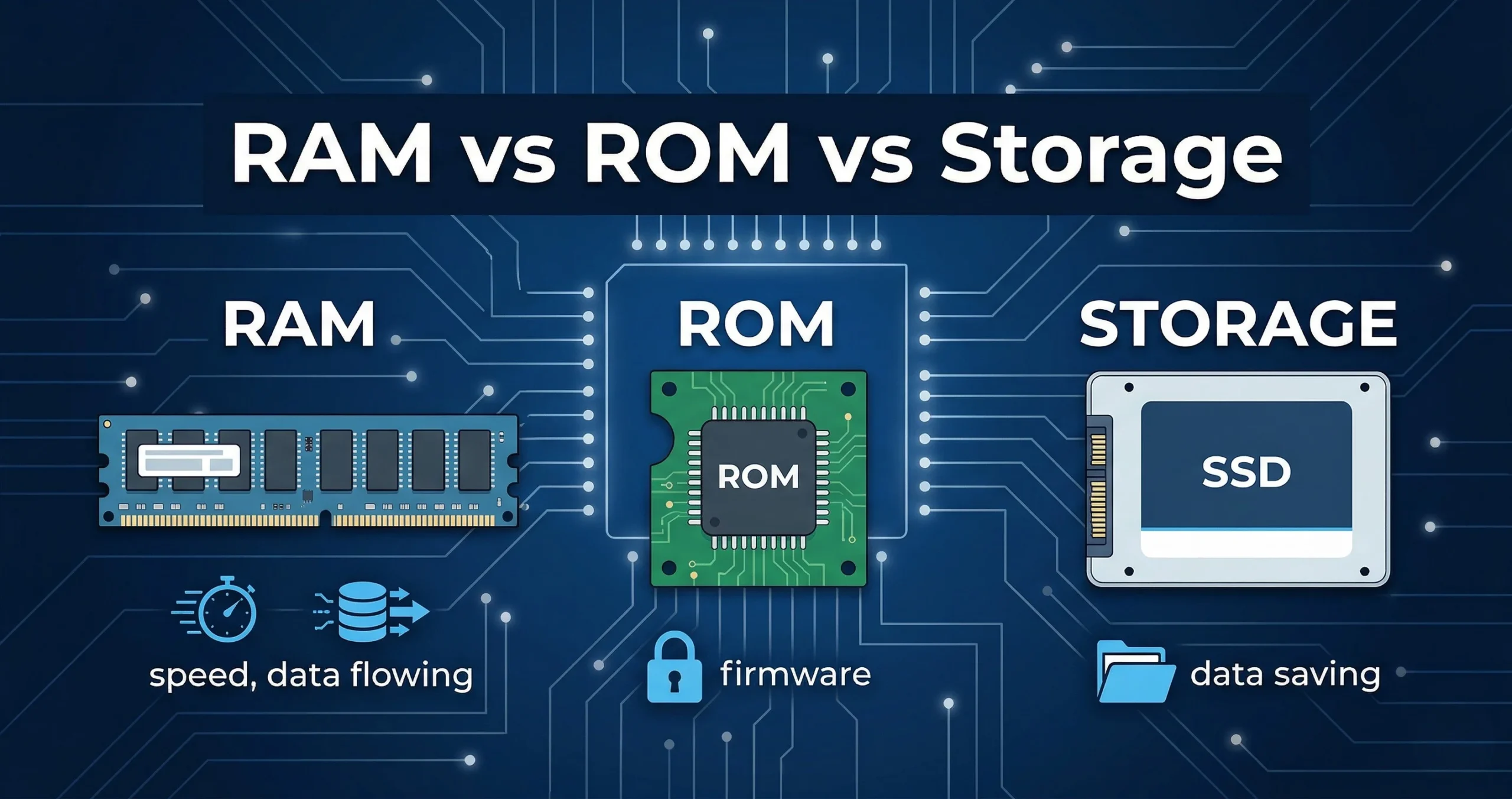
Sometimes you don’t even have to type in your password to become a victim. Merely visiting a compromised website can silently download Malware onto your device in the background. This is known as a “drive-by download.”
To prevent this, you should always keep your web browser and operating system updated to the latest versions. Modern browsers have excellent built-in defenses that will physically block you from entering known malicious sites. Combine these automated defenses with your new knowledge of how to check if a website is safe, and you create an incredibly strong shield against online criminals.
Take Control of Your Digital Safety
You hold the keys to your digital security, and navigating the web doesn’t have to feel like walking through a minefield. By pausing for just a few seconds to run these visual checks and utilize safety tools, you lock the door on cybercriminals and protect your peace of mind. Stay vigilant, trust your instincts when a deal looks too good to be true, and never let scammers have the last laugh.
Meta Description: Wondering how to check if a website is safe? Read our expert guide to spot fake links, avoid scams, use safety checkers, and browse the internet securely.